FireEye Network Security
Effective protection against cyber breaches for Mid-size to large organizations
FireEye Network Security
FireEye Network Security
is an effective cyber threat protection solution that helps organizations minimize the risk of costly breaches by accurately detecting and immediately stopping advanced, targeted and other evasive attacks hiding in Internet traffic. It facilitates efficient resolution of detected security incidents in minutes with concrete evidence, actionable intelligence and response work flow integration.
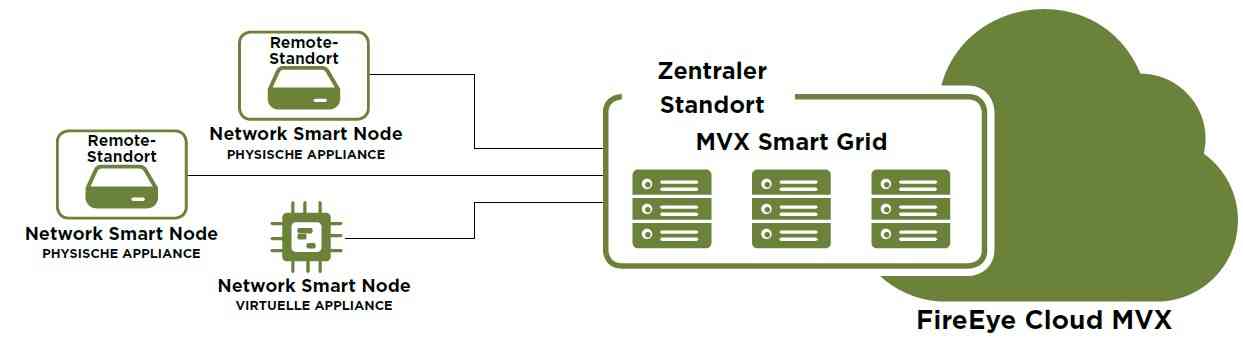
Distributed Network Security
At the core of FireEye Network Security are the Multi-Vector Virtual Execution (MVX) and Intelligence-Driven Analysis (IDA) technologies. MVX is a signature-less, dynamic analysis engine that inspects suspicious network traffic to identify attacks that evade traditional signature- and policy-based defenses. IDA is a collection of contextual, dynamic rules engines that detects and blocks malicious activity in real-time and retroactively, based on the latest machine-, attacker- and victim-intelligence. FireEye Network Security also includes intrusion prevention system (IPS) technology to detect common attacks using conventional signature matching.
Datasheet Order NowIKARUS Security Software Sales-Hotline:
Support - +1-650-273-5849 Sales - +1 -574-358-4378
»When it comes to detecting and preventing advanced attacks, the power of FireEye MVX technology has no competition.«
Wahid Hammami,
Chief Information Officer
Detect threats others miss
- Apply state of the art, Signatureless detection and protection against the most advanced threats, including zero-days.
- Combine heuristics, code analysis, statistical analysis, emulation, and machine learning in one advanced Sandboxing solution.
- Enhance detection efficacy with front line intelligence derived on the front lines of the worlds biggest breaches.
